Sensors | Free Full-Text | Cooperative Feedback Bits Allocation and Transmit Power Control in Underlay Cognitive Radio Networks

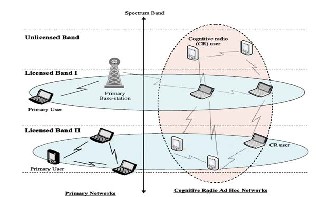
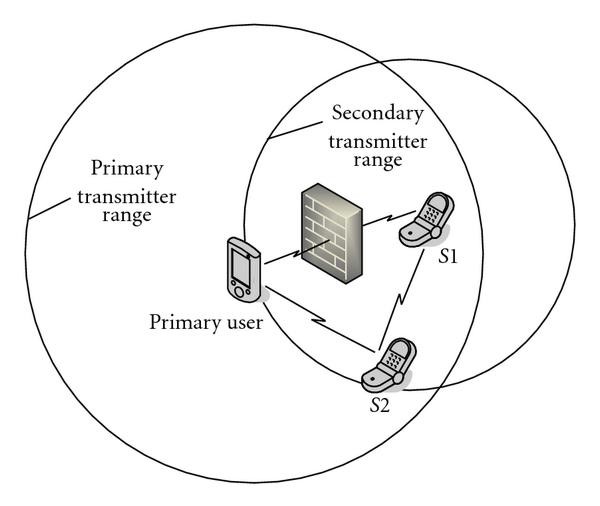
A Cognitive Radio Network Architecture with Primary and Secondary User... | Download Scientific Diagram
Analysis of spectrum allocation of secondary users based on linear cooperative spectrum sensing techniques in cognitive radio networks
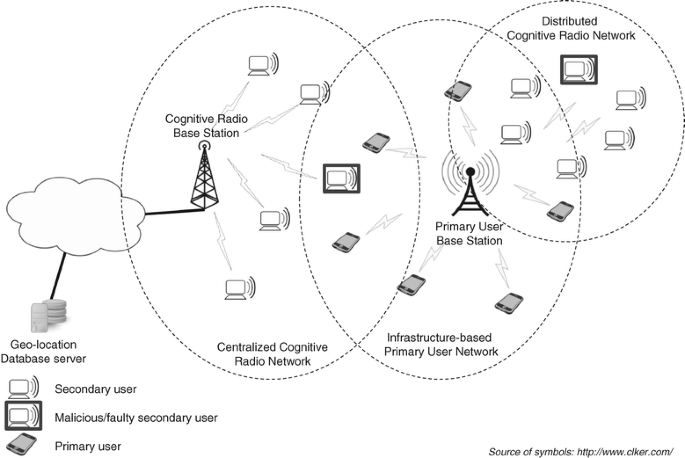
A survey on security attacks and countermeasures with primary user detection in cognitive radio networks | EURASIP Journal on Information Security | Full Text
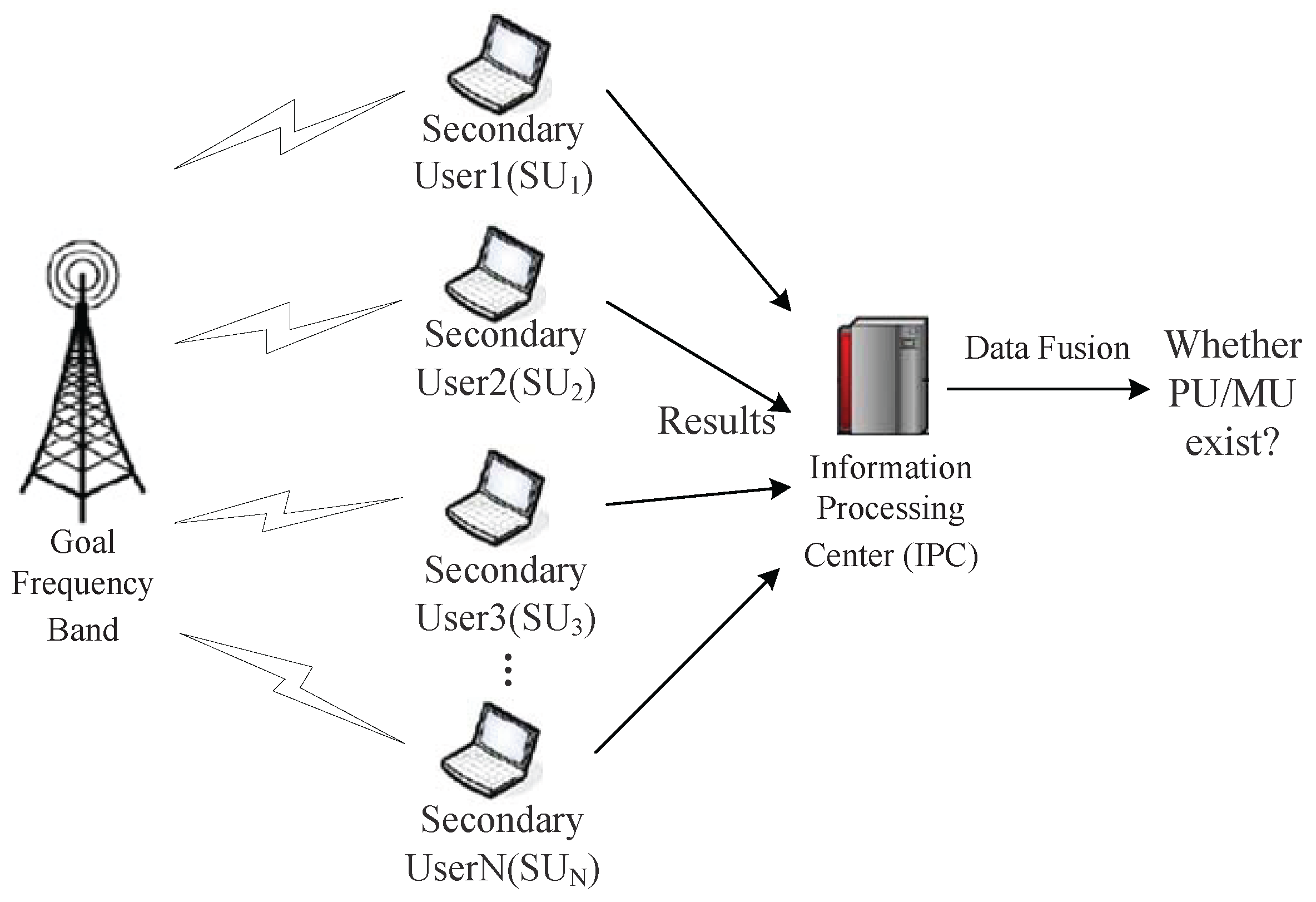
Algorithms | Free Full-Text | Primary User Localization Algorithm Based on Compressive Sensing in Cognitive Radio Networks
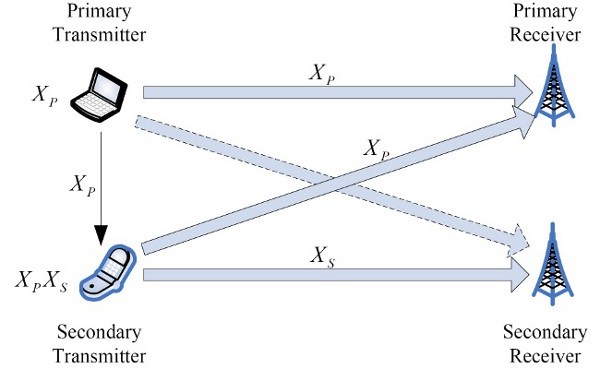
Cooperative Detection for Primary User in Cognitive Radio Networks | EURASIP Journal on Wireless Communications and Networking | Full Text

A Cognitive Radio Network Architecture with Primary and Secondary User... | Download Scientific Diagram

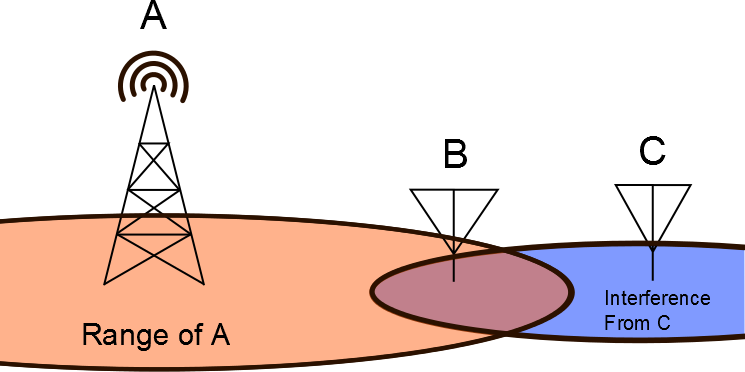
Sensors | Free Full-Text | Interference Spreading through Random Subcarrier Allocation Technique and Its Error Rate Performance in Cognitive Radio Networks

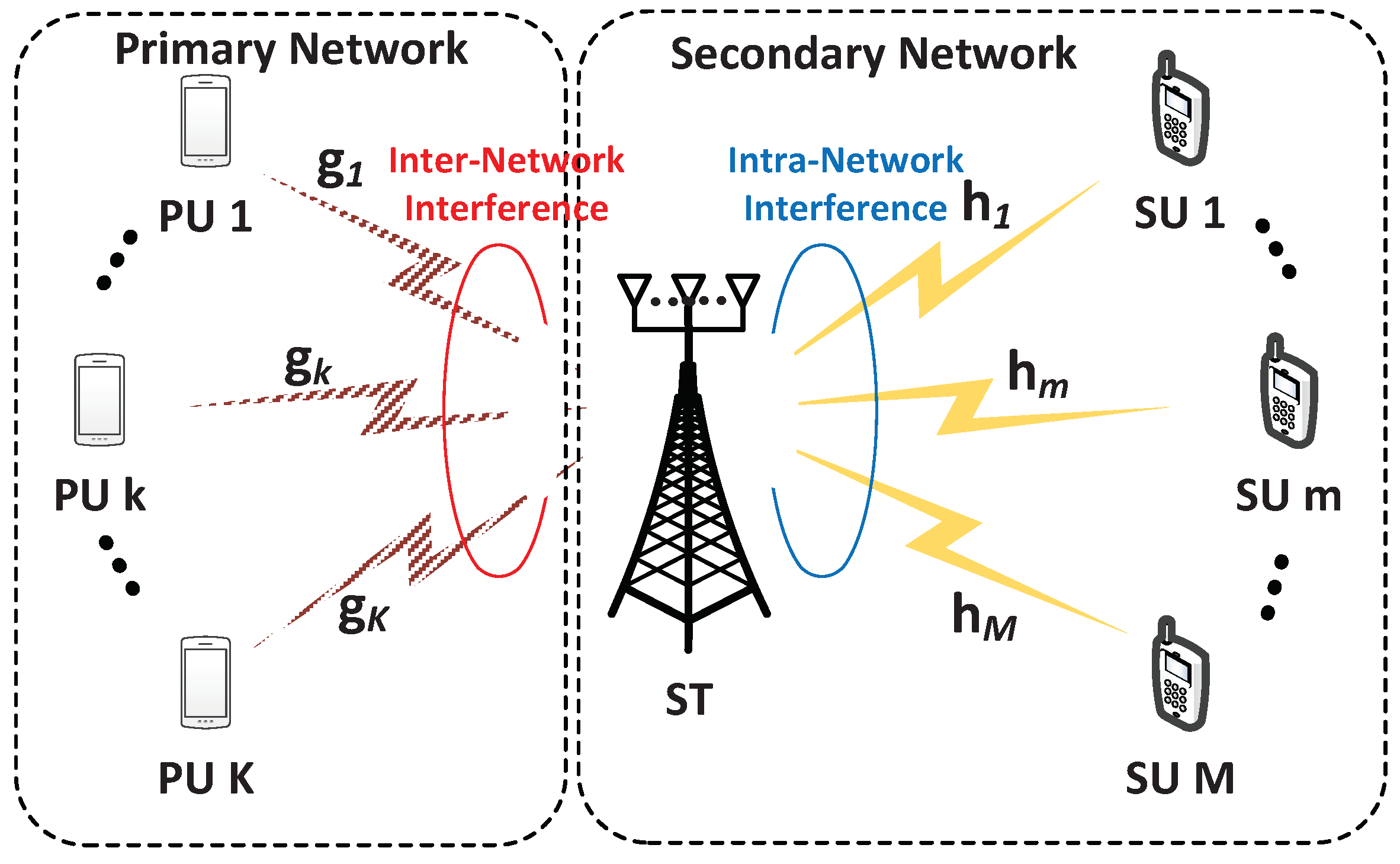
Optimized secondary user selection for quality of service enhancement of Two-Tier multi-user Cognitive Radio Network: A game theoretic approach - ScienceDirect

Performance Evaluation of Cognitive Radio Networks with Imperfect Spectrum Sensing and Bursty Primary User Traffic

Figure 1 from Energy-Infeasibility Tradeoff in Cognitive Radio Networks: Price-Driven Spectrum Access Algorithms | Semantic Scholar